Dr. Shaligram Parajuli elected President of CSRI Nepal. New Executive Team Set to Enhance Nepal’s Cybersecurity Framework
The Center for Cyber Security Research and Innovation (CSRI) Nepal elected its new Executive Committee. The appointments, made through an internal agreement, reflect the organization’s commitment to strengthening cybersecurity research, […]
Boost Your Content with Stunning Visuals: Discover the Top 5 Websites for Royalty Free Images
In today’s digital world, visual material is critical for catching attention and successfully expressing messages. Finding high-quality photos is vital for increasing your work, whether you are a blogger, website […]
Multi-stakeholder Discussion on Cyber Security Policy and Process is going to happen in Nepal
According to the press release released by Center for Cyber Security Research and Innovation, an event related to Cyber Security is going to be organized. Huawei’s main sponsor of the […]
Social Engineering Explained in Simple Way
Social engineering is the art of convincing people to reveal confidential information Common targets of social engineering include help desk personnel, technical support executives, system administrators, etc. Social engineers depend […]
What is Sniffing?
Network Sniffing Sniffing is a process of monitoring and capturing all data packets passing through a given network using sniffing tools. It is a form of wiretap applied to computer […]
Malware Threats in Cyber Security. What actually it is?
Malware Overview Malware is a malicious software that damages or disables computer systems and gives limited or full control of the systems to the malware creator for the purpose of […]
System Hacking. Here is how your system can be hacked
What is system hacking? System hacking is defined as the compromise of computer systems and software to access the target computer and steal or misuse their sensitive information. Here the […]
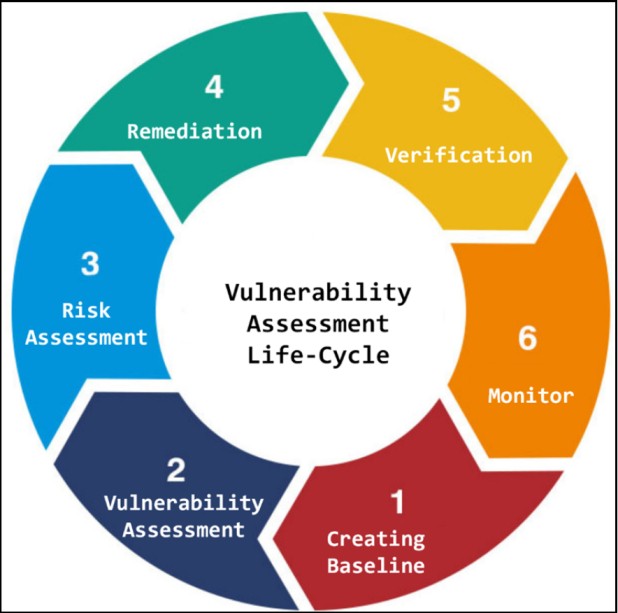
Cyber Security Vulnerability Assessment
Vulnerability analysis is the next phase of Ethical hacking to identify the security holes or vulnerabilities in your system or network. A vulnerability assessment is a process of defining, identifying, […]
Enumeration in Cyber Security! Everything that you need to understand.
What is Enumeration? In the enumeration phase, attacker creates active connections to system and performs directed queries to gain more information about the target. Attackers use extracted information to identify […]