Last Updated on by Sumi
What is phishing?
Phishing attacks is a hacking technique or trick that criminals use via an email to collect your personal data and information such as email addresses, passwords, credit card number and many more.
It is one of the oldest methodologies but yet very efficient technique practiced till date.
It is the simplest technique that hackers had already ready-made kits available on the dark web for amateur hackers.
This technique emerged in the mid-90s. Hackers used to target AOL users to share their log-in details.
Nowadays hackers target much more sensitive data like bank accounts information and passwords of online banking.
This technique is also used to collect information to sell for profit and earn money. It is also used to blackmail the peoples with their private information.
Types of Phishing Attack Techniques
There are 3 major techniques that hackers use to steal your information:
#1. Email Phishing
Email Phishing is the most popular technique where email is sent by the hackers to get your information.
Hackers register the domain closely related to the original email. Then hacker uses that email to send you fake emails in a real way. They make the simple scenario in such a way that recipients get convinced to provide their information.
Another way is also there where email contains malicious links and malware that infects your device.
The most complex and common email phishing technique is also there whre email contains links to fake websites.
Then the website collects the sensitive login information which is used to commit other cybercrimes.
How to dodge email phishing?
Fake emails are easy to spot if you look carefully. The domain name and email address look real but there is always something different.
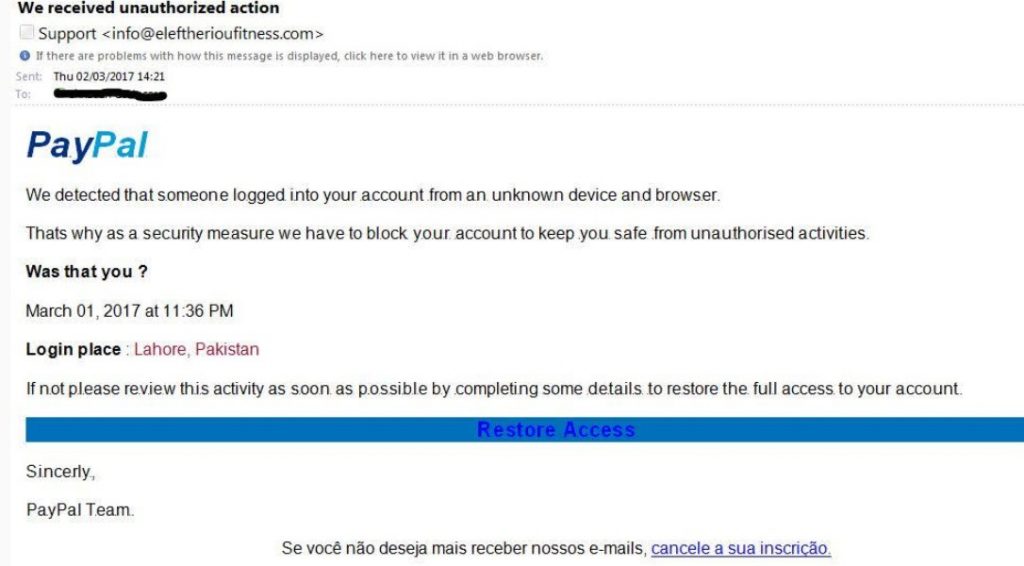
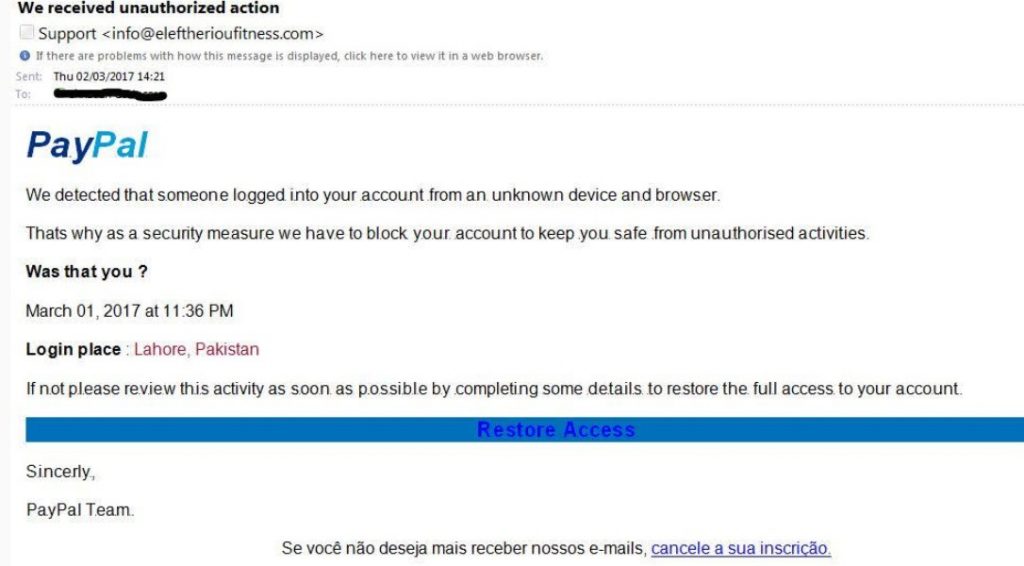
Things to look out includes :
- Public email domains
- Misspelled domain names
- Bad grammar and spelling
- Suspicious attachments/links
- Sense of urgency
To be careful about email phishing you should always avoid clicking on links attached to the email. If the email asks you to login direct go to the website and login with the credentials there.
#2. Website Phishing
Many of the websites are specially designed for phishing purposes. They look like popular websites which deals with sensitive issues such as private communications and transactions about finance.
There are 2 ways for website phishing. One where hackers track and get the login credentials after they visit fake websites.
Another one is where hackers infect users browsers with malware and spyware programs.
How to dodge website phishing?
The website URL of fake sites is not secured, that they doesnt contains HTTP and HTTPS prefixes.
Similarly, there are always some pages either inactive or superficial.
The best way to prevent this is to employ a decent cybersecurity program in the browsers that suspect the malware.
#3. Telephone Phishing
Telephone phishing is all about smooth talking to the publicly listed caller IDs. They usually get the numbers from bank books.
They make a trick to ask the credentials by requesting the account numbers and other information so as to fix the alleged problem in their bank account.
Unsuspecting victims users trust the words and share the information on the phone.
How to dodge telephone phishing?
The best way to prevent telephone phishing never shares your personal information on the telephone with anyone. Always verify the identity you are speaking to before talking about any personal pieces of information.
How to mitigate phishing attacks?
- Implement appropriate technical measures
- Learn the psychological triggers
- Build a positive security culture
- Train your staff
- Test the effectiveness of the training
Keep following ICTByte for similar updates.

