Last Updated on by ICT Byte
Cyber Security Context in Nepal, the event organized by the Center For Cyber Security Research and Innovation (CSRI) and Information Security Response Team Nepal (npCert) in association with Nepal Telecommunications Authority, CSIT Association of Nepal and CAN Federation was successfully conducted today, Tuesday at 3 pm.
This event was hosted to focus on the Cyber Security Context in Nepal (Past / Present/way) with the resource person Mr. Narayan Koirala. He is a Software Engineer along with an MBA degree. He is also a certified ISO 27001:2013 Auditor and a certified CISCO CCNA CyberOps professional. Besides, he is associated with the Nepalese Young Entrepreneurs’ Forum (NYEF), Lions Club International, and CAN Federation.


Mr. Koirala has been featured in numerous National and International Media and shared his thoughts about rising cybercrime and prevention in various conferences/ events. His articles about Cyber Hygiene and Data Security in the fast-paced technological advancement are being followed by many individuals and organizations.
With all his experiences and knowledge it was a pleasure to listen to his thoughts about the Cyber Security context in Nepal. Here is the short summary of the event that he had shared with us.
Summary of Event
Digital Assets
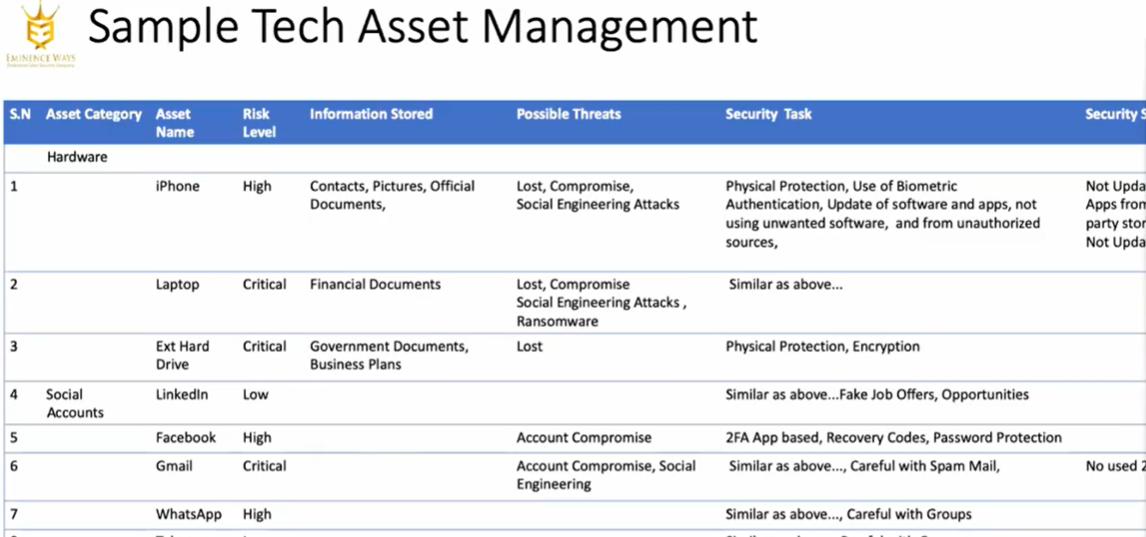
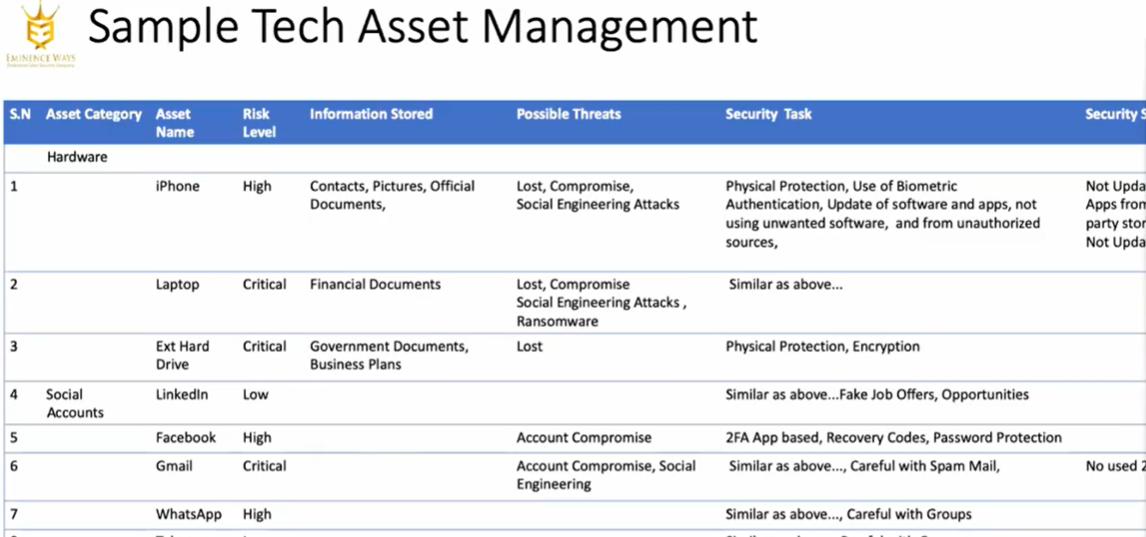
According to him, Individuals should know about their digital assets like hardware, software, software access, and social accounts that they use. Then only they can focus on how to secure the assets that are at the organizational level.
Pillars of Cybersecurity
The three basic pillars of Cybersecurity are;
- People
- Technology
- Process


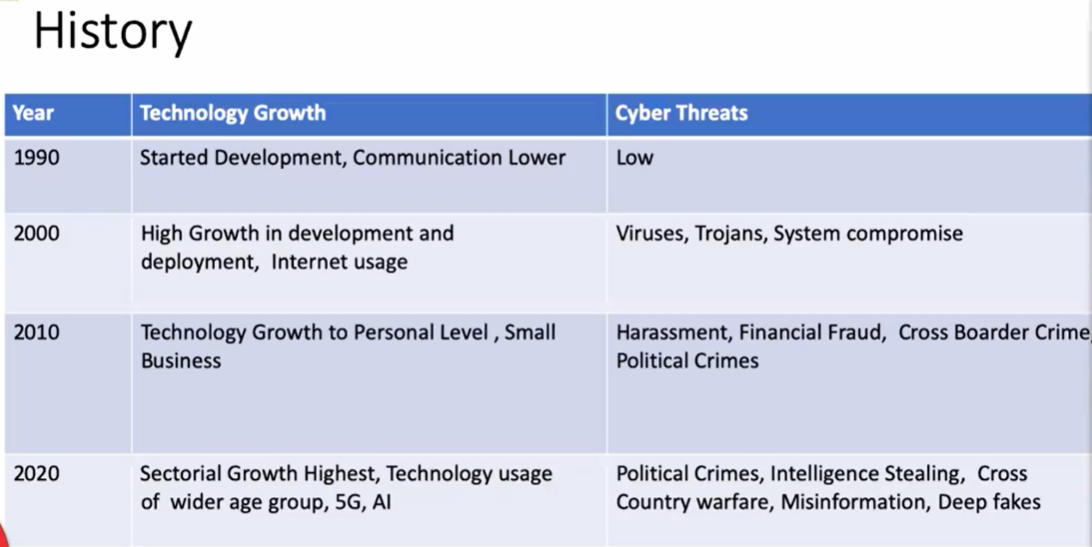
History of CyberSecurity
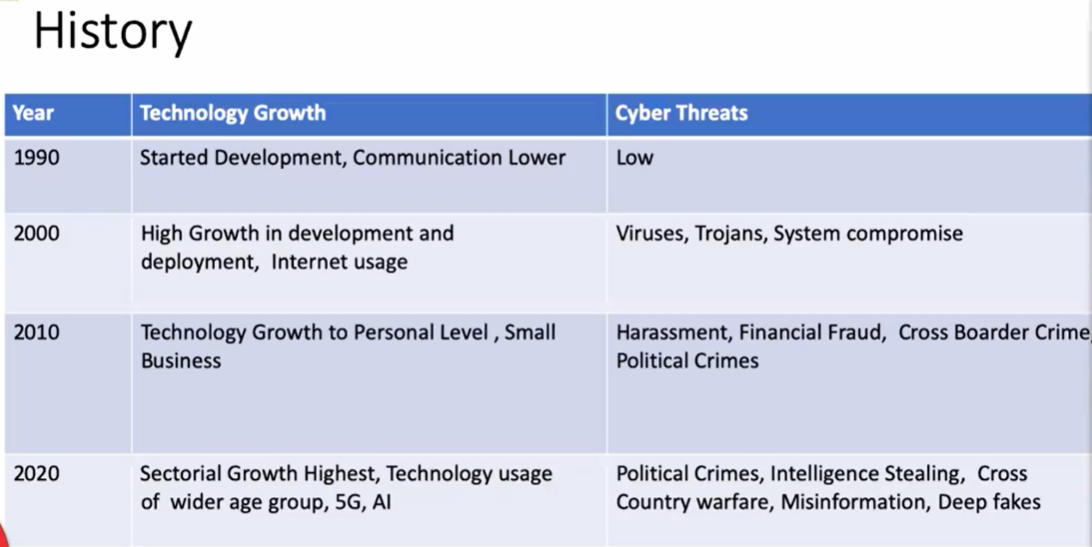
- In the early 1990s when technology just started its growth there was a very low risk of cyber threats.
- Later with the high growth in development and deployment, there was an increase in internet usage in the year 2000. With that growth came several viruses, trojans in the system.
- Similarly, the advancement in technology also brought cyber threats like Financial Fraud, Cross Border Crime, political crime in the 2010s.
- The current Scenario in 2020 seems to have more cyber threats than late histories like Intelligent Stealing, Cross country warfare, Deep fakes, and more political crimes and issues.
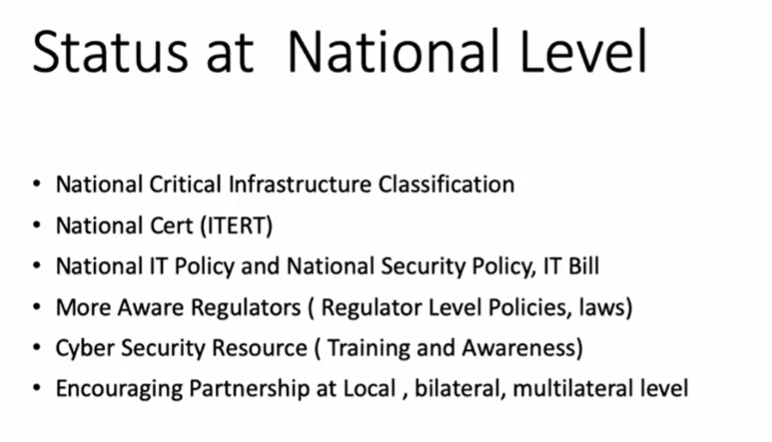
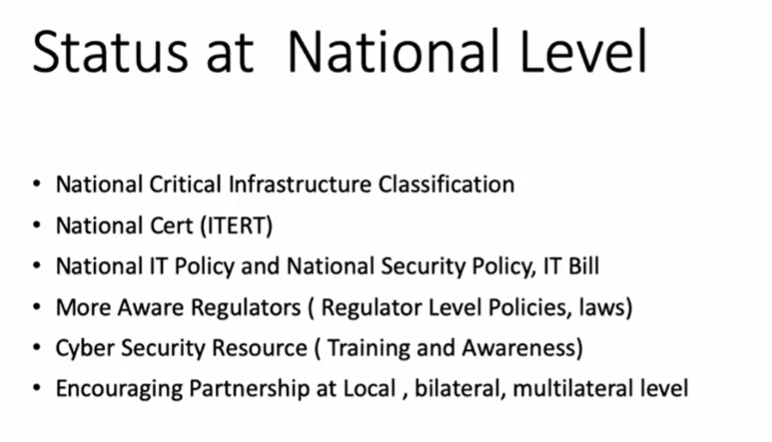
Current status of CyberSecurity in Nepal
#1. Information Technology Landscape
- Growth in Development and Deployment of IT systems
- Use of modern-day technologies for personal and professional life
- Ecommerce has revolutionalized the way
- Rise in the digital payment ecosystem.
#2. Common Attack Surface
- Communication channel
- Software Application
- Network Infrastructure
- Server/system
- people
#3. Limited understanding of Tech assests and risk areas
#4. Ignorance of people towards protection of assests/goodwill(knowledge vs practice)
#5. Existence of process but poor execution
#6.Ignorance towards cyber security by organizations
#7. Weak governance(national/institutional)
#8. Less preparance in Incident Handling
#9. Less prepared in continuos monitoring of assets and behaviour
Future of CyberSecurity
Major threats seems to be in;
- Social Engineering Attacks
- Targeted Ransomware Attacks
- Remote Worker Endpoint Security
- Cloud Security
- API Level attacks
- Misinformation and Deep fakes
- Mobile Malware/ Attacks
- 5G to Wifi Breaches
Threats as per sector
- Healthcare
- Telecommunication
- Government
- Media
- Education
Threat target
- Biological and Chemical Warfare
- Cyber Warfare
Solutions/ Things we should consider for CyberSecurity in Nepal
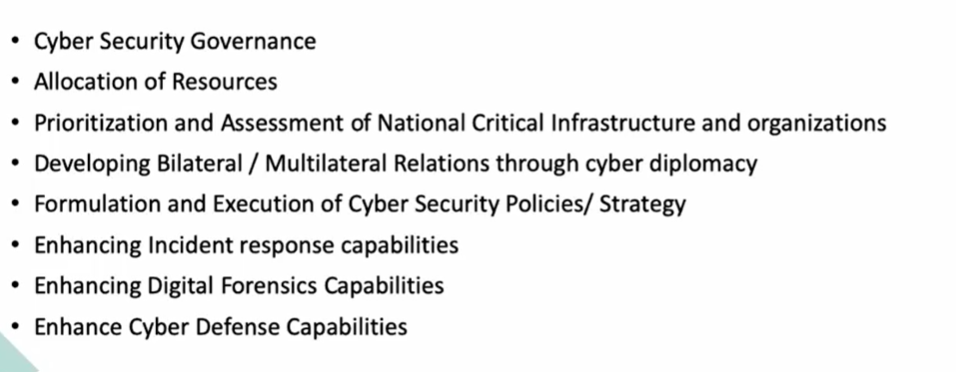
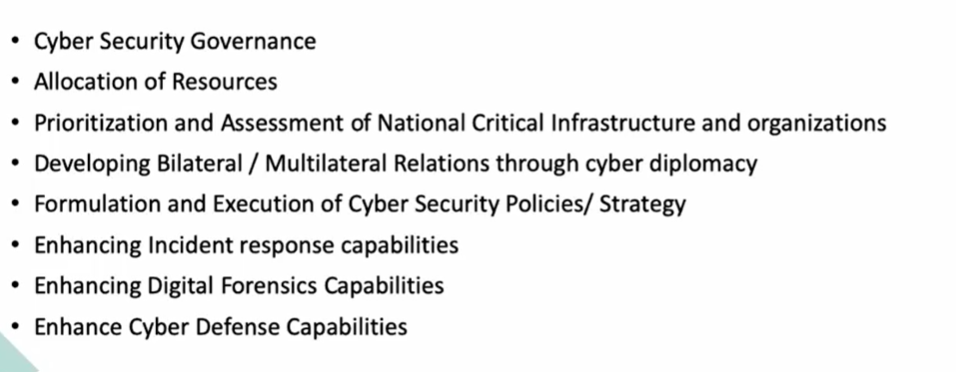
360 View of Cyber Security


Conclusion
There is massive opportunity ahead at various subdomains of CyberSecurity.
Some of the Queries by Audience
What are the counter measurements for defending threads and vulnerabilities in College/ Campus Level?
It depends on level of protection that college level is trying to solve. That may be network level or Software level. For Network level, go with Firewall defense mechanism and system updates while for software level go with OS level fixation.
Cyber Security career scope for students in Nepal
He suggested to start from the Software development level. One should have proper knowledge from building software to breaking the software to properly build a secure system and fix the issues. So, better to make a base in the knowledge of the software industry to dive into the various scopes of Cyber Security.
Question by Prof. Subarna Shakya- What are the Scopes of Security Audit and how much investment does it require?
-Conceptual Knowledge is required as an investment to audit.
-Investment as in for Knowledge and resource person is required.
Lastly, with all this, the event was successfully conducted with the certification of recognition and appreciation to the resource Speaker Mr. Narayan Koirala.
If you have missed the live event, here is the attached video ;