Last Updated on by Sumi
Ethical hacking is one of the important elements of the technology world. It helps us detect vulnerability in the system and find ways to fix it. It is important so that we can stop possible future hackings by hackers. Here, we have come up with a hacker toolkit i.e. the best software for hacking purposes. This hacking tool includes port scanners, web vulnerability scanner, forensic tools, password crackers, traffic analysis, and social engineering tools.
List of Hacking tools For Windows, Linux, macOS
- Metasploit
- Acunetix WVS
- NMap
- Wireshark
- oclHashcat
- Nessus
- Maltego
- Social -Engineer Toolkit
- Netsparker
- w3af
- John The Ripper
- Aircrack-ng
- Ghidra
Metasploit
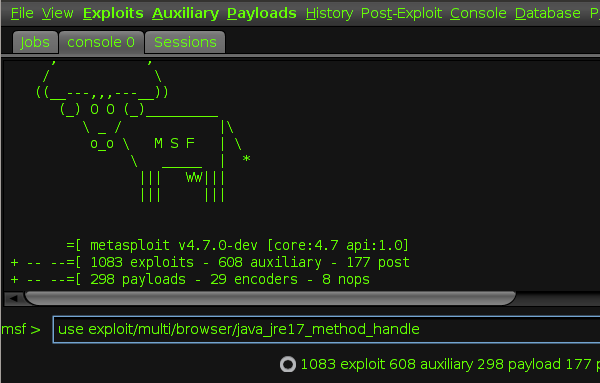
Metasploit is a hacking tool that allows you to find, exploit, and validate vulnerabilities in the system. Moreover, you can also use this to make your own custom tools. It is one of the most popular cybersecurity tools to detect vulnerabilities. In addition, this tool is backed by more than 200,000 users and contributors, and they will help you to get insights and uncover the weaknesses in your system. This tool simulates real-world attacks and finds the weak points in your system.
Go to website and download: Click here
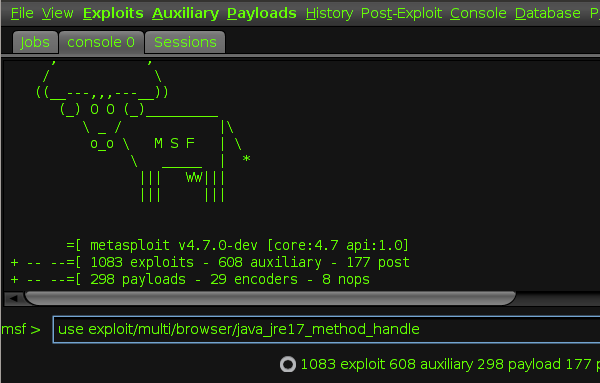
Acunetix WVS
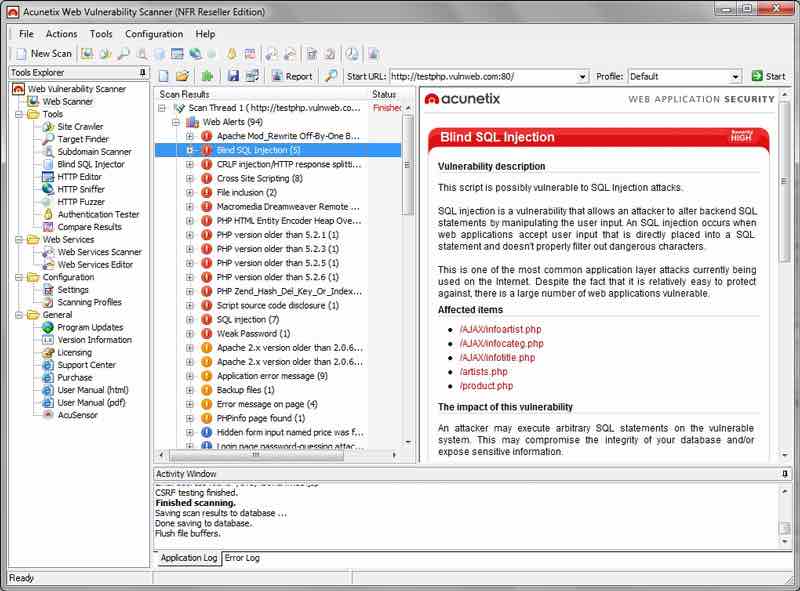
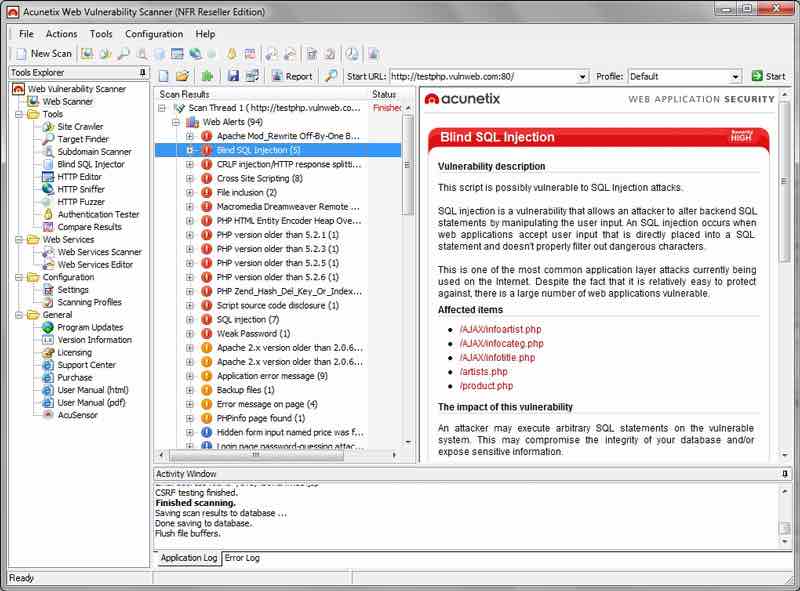
Acunetix is a web vulnerability scanner (WVS) that scans a website and find vulnerabilities in it that could prove fatal. This tool finds out malicious Cross-site Scripting, SQL injection, and other vulnerabilities by crawling the website. This tool has the highest rate of detection of vulnerabilities in WordPress websites. In addition, this tool allows you to access the password-protected areas of websites as it comes with a Login Sequence Recorder.
Go to website and download: Click here
Nmap
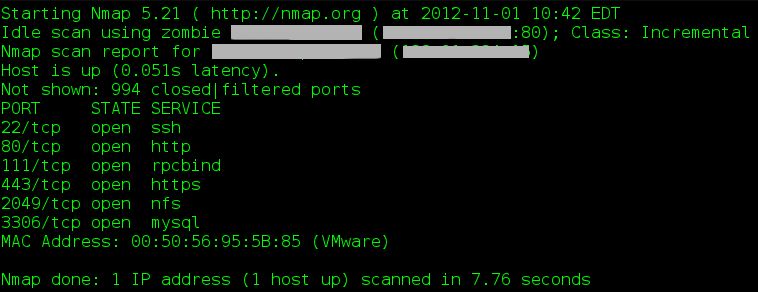
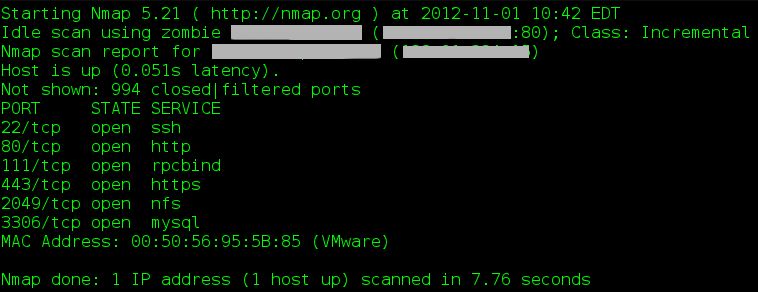
Nmap, also known as Network Mapper is a port scanner tool for efficient network discovery and security auditing. It provides the most accurate port status of a system’s internet footprint by testing servers, firewalls, and network perimeters with Nmap online. Nmap uses raw IP packets to determine various information about the network. It determines the hosts available on a network, their services along with details, operating systems used by hosts, the type of firewall used, and other information. Nmap is one of the most popular hacking tools and it has won multiple security products of the year awards as well.
Go to website and download: Click here
Wireshark
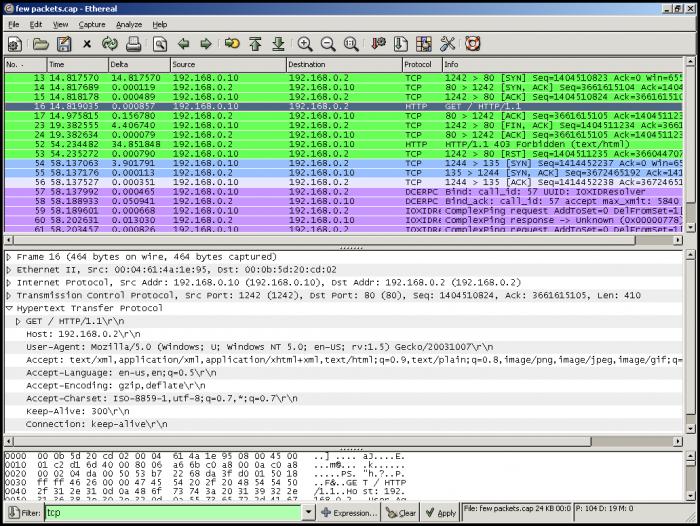
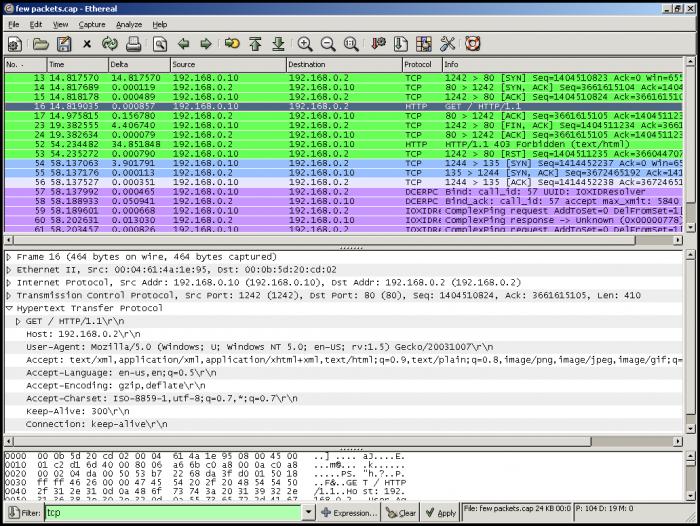
Wireshark is a very popular packet analyzer. It probes firewall rule-sets by discovering vulnerability within a network. It performs a deep scan of hundreds of protocols. In addition, it is also used to analyze networks and capture live packets. The main use of Wireshark is that it helps you to read live data from Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI, and others. Originally, this tool was named Ethereal. Moreover, Wireshark also comes in a command-line version and it is called the TShark.
Go to website and download: Click here
oclHashcat
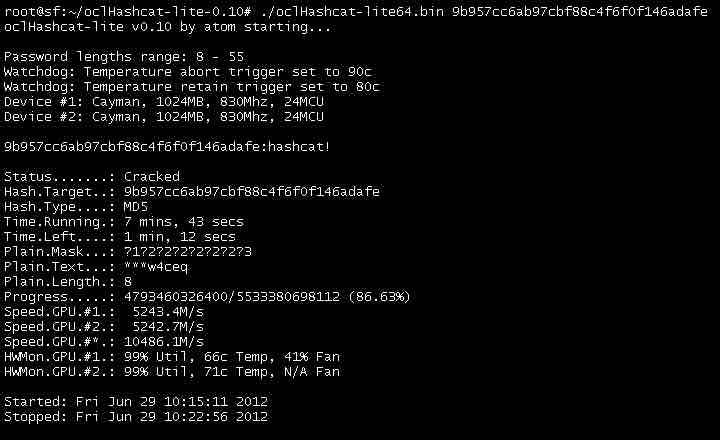
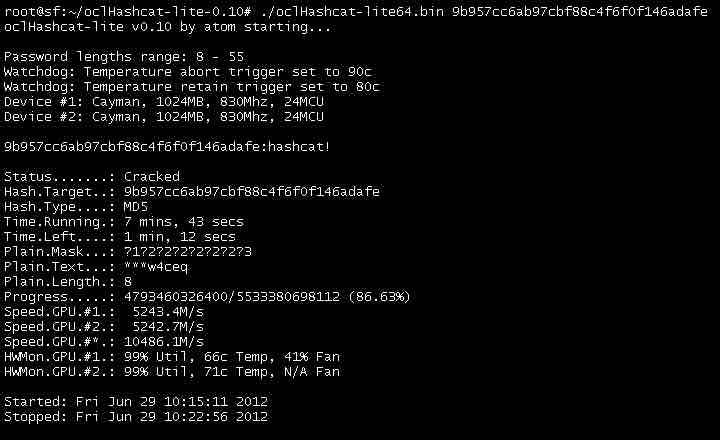
Many of you may be familiar with Hashcat which is a CPU-based hacking tool to crack passwords. Similarly, oclHashcat is an advanced version password cracking tool based on the power of the GPU. This tool is renowned as one of the fastest password cracking tools available right now. It uses various attack modes such as straight, combination, brute-force, and many more for cracking passwords.
Go to website and download: Click here
Nessus
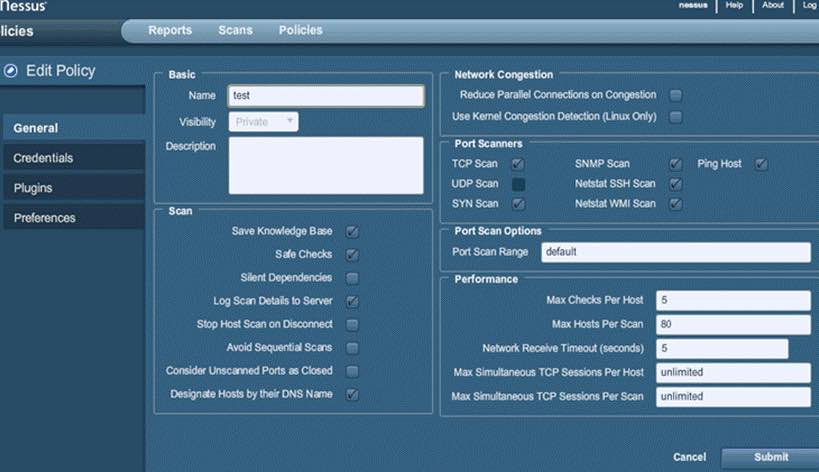
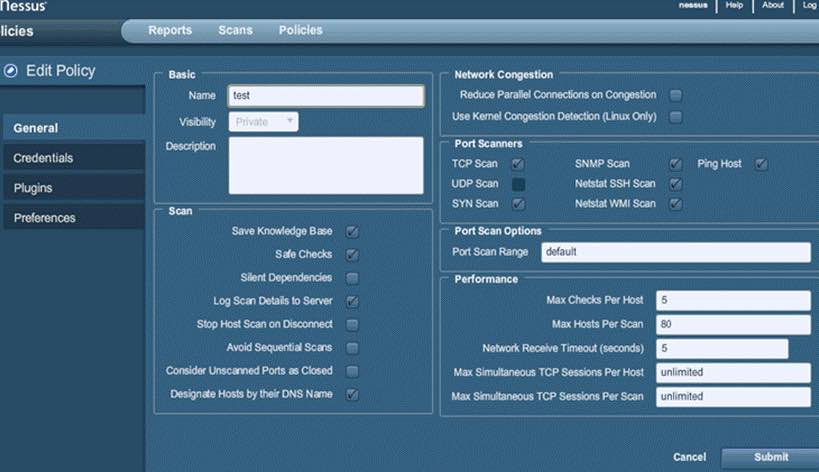
Tenable Network Security developed one of the best free security tool called Nessus that works with the help of a client-server framework. It is a vulnerability scanner and serves different purposes to different types of users – Nessus Home, Nessus Professional, Nessus Manager, and Nessus Cloud. Nessus can detect multiple vulnerabilities including remote access flaw detection, misconfiguration alert, denial of services against TCP/IP stack, preparation of PCI DSS audits, malware detection, sensitive data searches, etc. In addition, Nessus can also call a popular tool called Hydra externally to launch a dictionary attack.
Go to website and download: Click here
Maltego
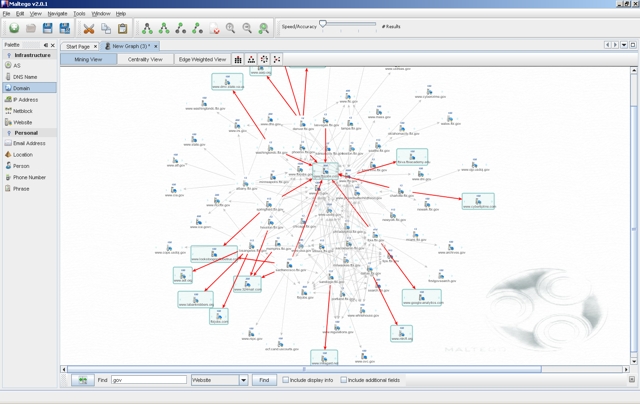
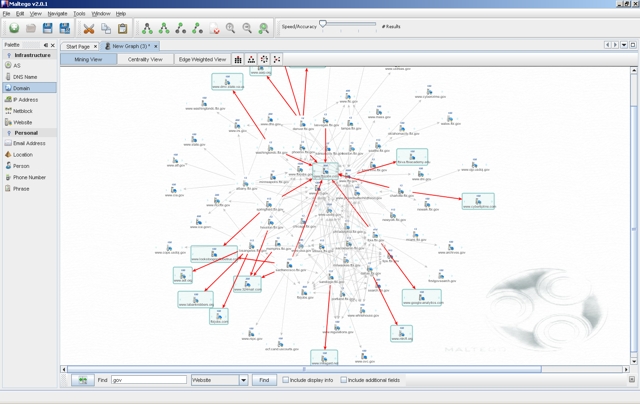
Maltego is one of the best open-source hacking tools for the forensics platform. This tool works by collecting data from various open sources, transforming, and visualizing it in graph format. This information will be useful for link analysis and data mining. This tool is based on Java with an easy-to-use GUI as well. This tool conducts the online investigation and finds relationships between information from various sources located on the internet.
Maltego has three versions: Maltego CE, Maltego Classic and Maltego XL.
Go to website and download: Click here
Also read: The Best Programming Languages for Linux Lovers
Social – Engineer Toolkit
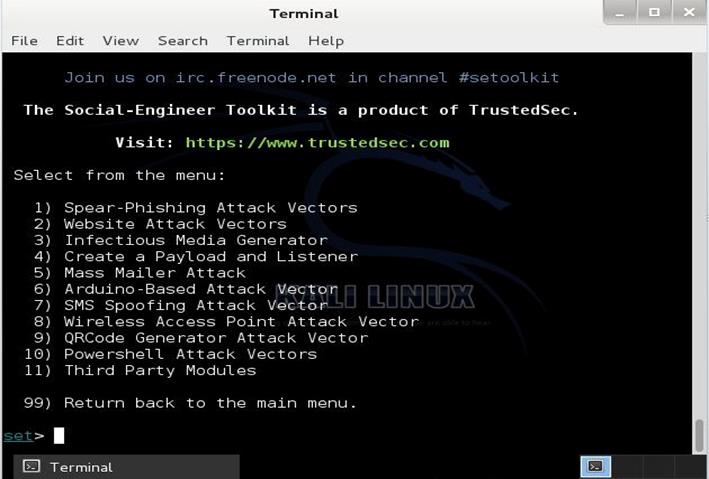
Social-Engineer Toolkit is a python-driven hacking tool by TrustedSec. It is used for simulating multiple types of social engineering attacks. Moreover, Mr. Robot also featured this toolkit where we see Elliot sing the SMS spoofing tool from the Social-Engineer Toolkit. It stimulates attacks such as credential harvestings, phishing attacks, and more.
Downloaded more than 2 million times, this tool is the go-to tool for social engineering penetration tests. It works by automating the attacks, generating disguising emails, web pages and many more.
This tool is compatible with Linux systems. However, it is only partially supported on Mac OS X and Windows.
To download, go to Linux and type the following command:
git clone https://github.com/trustedsec/social-engineer-toolkit/ set/
Netsparker
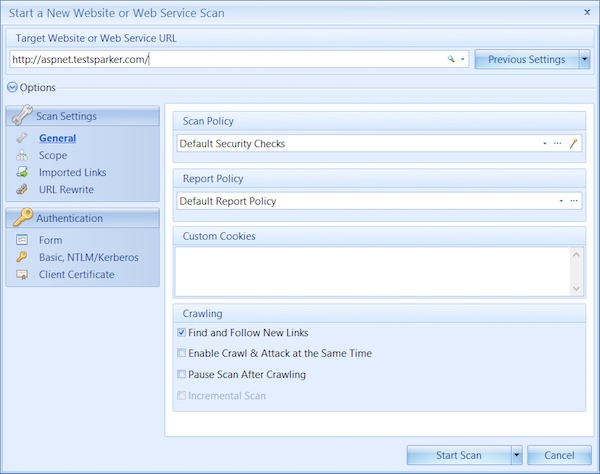
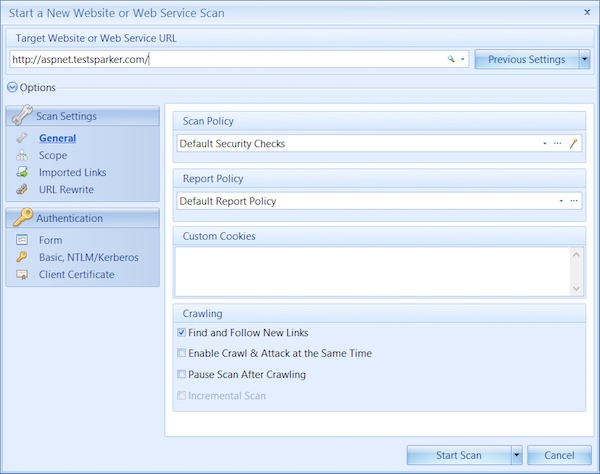
Netsparker is a web application scanner that scans the web applications for vulnerabilities like SQL Injection and Cross-site Scripting (XSS). Moreover, the platform and the technology used for building the apps do not affect this tool. In addition, it also suggests remedial actions in a read-only and safe way. You don’t need to verify the vulnerability by yourself since this tool produces a proof of exploitation as well. Even if it cannot verify the vulnerability by itself, it will notify you. This tool also supports JavaScript and AJAX-based applications. This means that you don’t need to configure the scanner to scan different types of web applications.
This application is available for Windows only.
Go to website and download: Click here
w3af
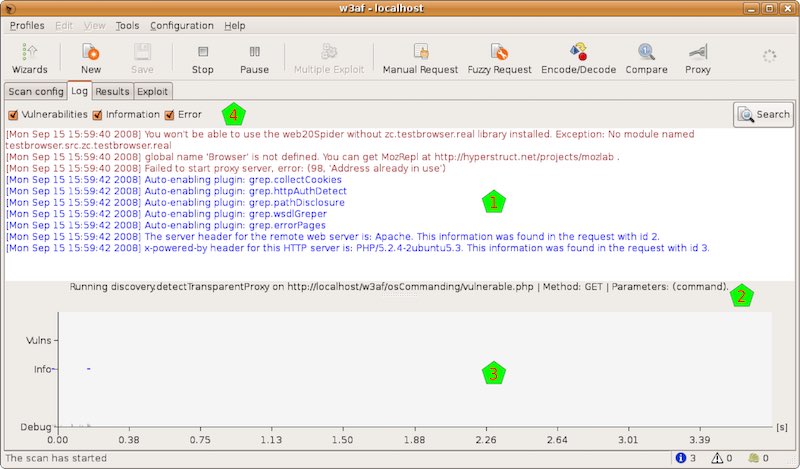
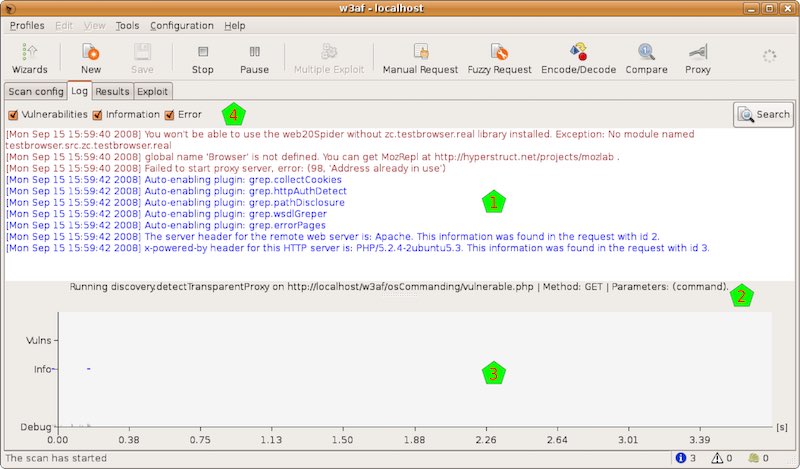
w3af (web application attack and audit framework) is also a web application security scanner. It is very popular among hackers and penetration testers. With the help of this tool, you can get security vulnerability information that you can further use in penetration testing engagements. This tool also claims to identify more than 200 vulnerabilities in web applications. These vulnerabilities include cross-site scripting, SQL Injection, PHP misconfigurations, guessable credentials, and unhandled application errors.
This tool is available in both the command line and in GUI so you can use whichever you want to. There is a pre-defined profile for beginners to use. And, by using this profile, you can audit a web app in less than 5 clicks.
This tool is available for Linux, BSD, and OS X. Windows only support the older versions.
Go to website and download: Click here
John The Ripper
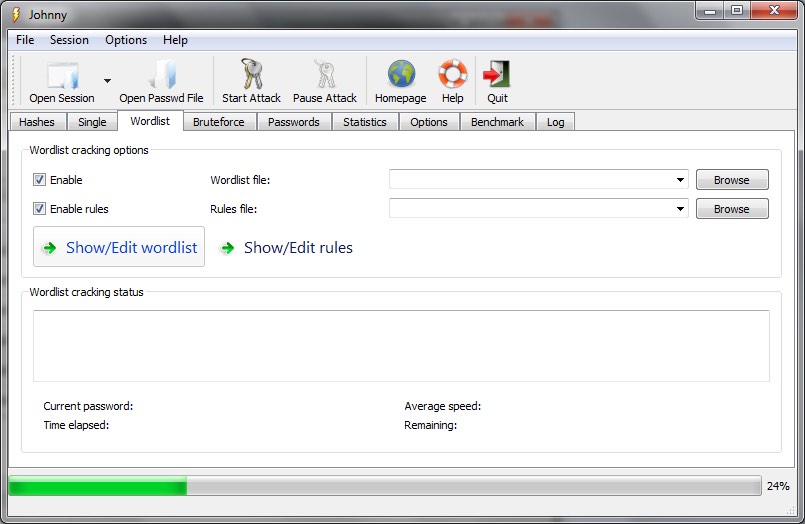
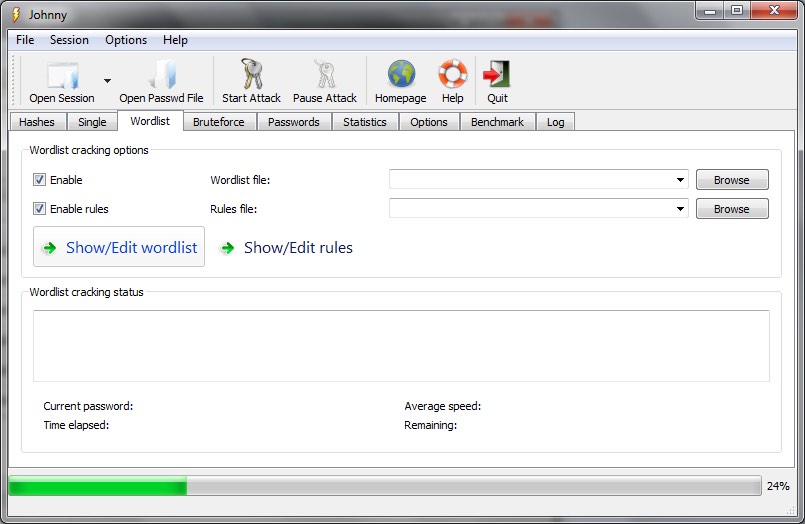
Most people interested in ethical hacking must have at least heard of John The Ripper. This is free and open-source software and it is distributed in the form of source code. This software is primarily written in C language. Also, this hacking tool is a combination of multiple password crackers into one. Therefore, different modules present in the software provides it the ability to crack the passwords using different encryption techniques.
This is one of the hacking tools that is available in most of the platforms inlcuding Linux, Windows, DOS, OpenVMS, and Unix.
Go to website and download: Click here
Aircrack-ng
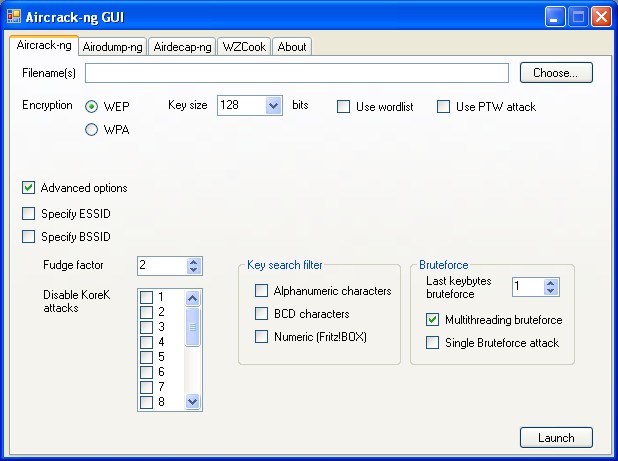
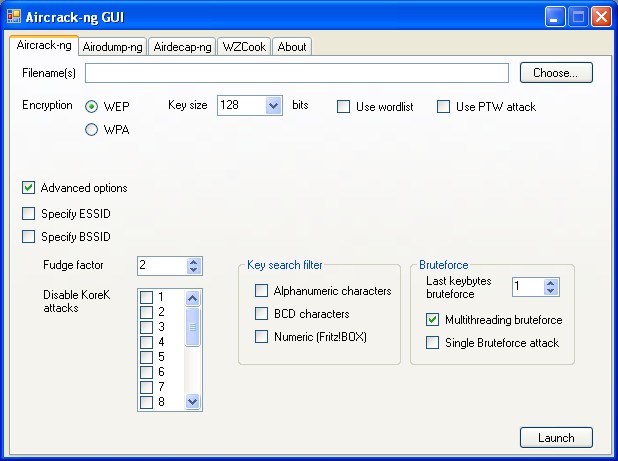
Aircrack-ng is another one of the hacking tools that you use for password cracking. The Aircrack-ng replaces the older Aircrack, and the ng in Aircrack-ng stands for ‘new generation’. It is a network suite and it consists of a detector, traffic sniffer, and password cracker tool. In addition, these tools are based on the command line and allow heavy scripting. It can be used for monitoring, attacking, testing, and cracking Wi-Fi security.
It is available for different platforms including macOS, Linux, FreeBSD, and Windows.
Go to website and download: Click here
Ghidra


Ghidra is a reverse engineering tool by NSA and they recently open-sourced the tool. NSA has used this software for more than a decade. This tool can be used to detect vulnerabilities that can be exploited. It is done by digging deep into the malware and software.
What is more important about this tool is that it has multi-user support. Because of this feature, researchers can collaborate and reverse engineer a single binary. You can also create your own Ghidra plugin add-ons for extra functionality by using the exposed API.
It is available for Mac OS, Linux, and Windows.
Go to website and download: Click here

