What are Wireless Network Threats and its Measures?
Last Updated on by Sarina Sindurakar
Introduction
Wireless networks, and the wireless devices that use them, introduce a host of security problems over and above those found in wired networks. Some of the key factors contributing to the higher security risk of wireless networks compared to wired networks include the following:
- Channel: Wireless networking typically involves broadcast communications, which is far more susceptible to eavesdropping and jamming than wired networks. Wireless networks are also more vulnerable to active attacks that exploit vulnerabilities in communications protocols.
- Mobility: Wireless devices are, in principle and usually in practice, far more portable and mobile than wired devices. This mobility results in several risks described subsequently.
- Resources: Some wireless devices, such as smartphones and tablets, have sophisticated operating systems but limited memory and processing resources with which to counter threats, including denial of service and malware.
- Accessibility: Some wireless devices, such as sensors and robots, may be left unattended in remote and/or hostile locations. This greatly increases their vulnerability to physical attacks.
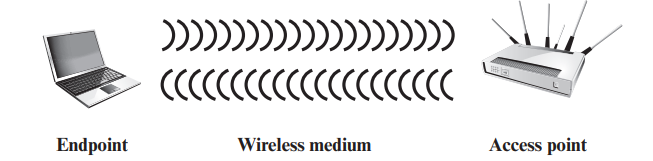
In simple terms, the wireless environment consists of three components that provide a point of attack. The wireless client can be a cell phone, a Wi-Fi–enabled laptop or tablet, a wireless sensor, a Bluetooth device, and so on. The wireless access point provides a connection to the network or service. Examples of access points are cell towers, Wi-Fi hotspots, and wireless access points to wired local or wide area networks. The transmission medium, which carries the radio waves for data transfer, is also a source of vulnerability.
Wireless Network Threats
The following are security threats to wireless networks:
- Malicious association: In this situation, a wireless device is configured to appear to be a legitimate access point, enabling the operator to steal passwords from legitimate users and then penetrate a wired network through a legitimate wireless access point.
- Ad hoc networks: These are peer-to-peer networks between wireless computers with no access point between them. Such networks can pose a security threat due to a lack of a central point of control.
- Identity theft (MAC spoofing): This occurs when an attacker can eavesdrop on network traffic and identify the MAC address of a computer with network privileges.
- Man-in-the-middle attacks: In a broader sense, this attack involves persuading a user and an access point to believe that they are talking to each other when in fact the communication is going through an intermediate attacking device. Wireless networks are particularly vulnerable to such attacks.
- Denial of service (DoS): In the context of a wireless network, a DoS attack occurs when an attacker continually bombards a wireless access point or some other accessible wireless port with various protocol messages designed to consume system resources. The wireless environment lends itself to this type of attack because it is so easy for the attacker to direct multiple wireless messages at the target.
Also Read: Remote User Authentication Using Symmetric Encryption
Wireless Security Measures
Wireless security measures can be grouped into those dealing with wireless transmissions, wireless access points, and wireless networks (consisting of wireless routers and endpoints).
Securing Wireless Transmission
The principal threats to wireless transmission are eavesdropping, altering or inserting messages, and disruption. To deal with eavesdropping, two types of countermeasures are appropriate:
- Signal-hiding techniques: Organizations can take several measures to make it more difficult for an attacker to locate their wireless access points, including turning off service set identifier (SSID) broadcasting by wireless access points; assigning cryptic names to SSIDs; reducing signal strength to the lowest level that still provides requisite coverage; and locating wireless access points in the interior of the building, away from windows and exterior walls. Greater security can be achieved by the use of directional antennas and signal-shielding techniques.
- Encryption: Encryption of all wireless transmission is effective against eavesdropping to the extent that the encryption keys are secured.
The use of encryption and authentication protocols is the standard method of countering attempts to alter or insert transmissions.
Securing Wireless Access Points
The main threat involving wireless access points is unauthorized access to the network. The principal approach for preventing such access is the IEEE 802.1X standard for port-based network access control. The standard provides an authentication mechanism for devices wishing to attach to a LAN or wireless network. The use of 802.1X can prevent rogue access points and other unauthorized devices from becoming insecure backdoors.
Securing Wireless Networks
It recommends the following techniques for wireless network security:
- Use encryption. Wireless routers are typically equipped with built-in encryption mechanisms for router-to-router traffic.
- Use antivirus and antispyware software, and a firewall. These facilities should be enabled on all wireless network endpoints.
- Change the identifier on your router from the default. Again, this measure thwarts attackers who will attempt to gain access to a wireless network using default router identifiers.
- Change your router’s pre-set password for administration. This is another prudent step.
- Allow only specific computers to access your wireless network. A router can be configured to only communicate with approved MAC addresses. Of course, MAC addresses can be spoofed, so this is just one element of a security strategy.
Also Read: Federated Identity Management
Follow us on Facebook


